How Peer Discovery Works in Cryptocurrency Networks: Bitcoin vs Ethereum
 May, 15 2026
May, 15 2026
Imagine trying to join a massive global conversation, but you don’t know anyone’s phone number. You can’t just dial a central switchboard because there isn’t one. This is the exact problem every new node faces when it joins a cryptocurrency network. Without a central server to say, "Here are your friends," how does a computer find its way into the decentralized web? The answer lies in peer discovery, the invisible handshake that allows blockchain networks to function without a boss.
Peer discovery is the mechanism by which nodes locate and connect to other participating nodes. It is the foundation of the peer-to-peer (P2P) infrastructure. If this process fails, a node is isolated. If it works poorly, the network becomes vulnerable to attacks. Understanding this process reveals why blockchains are resilient, how they resist censorship, and where their hidden weaknesses lie.
The Core Problem: Finding Peers Without a Center
In traditional client-server models, like accessing a website or logging into an email account, the client knows exactly where the server lives. The Domain Name System (DNS) translates a human-readable name like "google.com" into an IP address. But in a decentralized system like Bitcoin or Ethereum, there is no single owner. No company hosts the "main" server. Every participant is equal.
This creates a chicken-and-egg problem for new nodes. To participate in consensus, validate transactions, and sync the ledger, a node must connect to existing peers. But to find those peers, it needs to already be connected. The solution is a bootstrapping process that relies on hardcoded hints, distributed lists, and trustless protocols. These methods ensure that even if half the internet goes dark, the remaining nodes can still find each other.
Why can't cryptocurrency nodes use standard DNS like websites?
Standard DNS relies on centralized registrars and authoritative servers controlled by organizations. In a decentralized cryptocurrency network, relying on a single entity to provide peer lists would create a point of failure and a potential censorship vector. Peer discovery mechanisms are designed to distribute this responsibility across the entire network.
Bitcoin’s Multi-Tiered Approach
Bitcoin uses a robust, multi-layered peer discovery system prioritizing resilience and decentralization since its inception in 2009. When a Bitcoin node starts for the first time with an empty address book, it doesn’t guess. It follows a strict hierarchy of fallbacks.
The primary method is querying DNS Seeds are hardcoded domain names maintained by community members that return IP addresses of active, publicly available full nodes. These seeds act as initial entry points. They include dynamic servers that automatically scan the network for active nodes and static servers manually updated by operators. Nodes typically look for peers on default ports, such as 8333 for the mainnet or 18333 for testnet.
If DNS queries fail-perhaps due to local network issues or seed downtime-the node falls back to hardcoded seed nodes. These are specific IP addresses embedded directly into the Bitcoin Core software code. As a final resort, users can manually configure trusted peers obtained from community forums, friends, or official documentation. This redundancy ensures that the network remains accessible even under adverse conditions.
The Cascading Effect of Address Sharing
Once a node connects to at least one peer, the reliance on centralized resources drops significantly. The node immediately sends a getaddr message to request information about other known peers. The connected peer responds with a list of IP addresses it has recently seen. The new node then attempts to connect to these additional addresses.
This creates a cascading discovery effect. Each newly discovered peer provides access to yet another set of addresses. Within minutes, a fresh node can build a comprehensive map of the local network topology. The system tracks detailed statistics for each peer, including availability, latency, reliability, and misbehavior scores. Proven reliable peers are prioritized over seed nodes, distributing the load and maximizing the efficiency of the P2P mesh.
| Feature | Bitcoin (DNS Seeds) | Ethereum 2.0 (discv5) |
|---|---|---|
| Primary Protocol | TCP-based connection with version handshakes | UDP-based Node Discovery Protocol v5.1 |
| Initial Bootstrap | Hardcoded DNS seeds and IP seeds | Ethereum Node Records (ENRs) and bootnodes |
| Network Model | Proof-of-Work focused, stable topology | Proof-of-Stake focused, dynamic subnets |
| Address Updates | Periodic sharing via getaddr messages | Frequent ENR updates reflecting real-time status |
| Censorship Resistance | High, due to redundant seed sources | High, due to cryptographic verification of records |
Ethereum 2.0 and the discv5 Protocol
Ethereum 2.0 employs a fundamentally different approach using the Node Discovery Protocol version 5.1 (discv5), optimized for Proof-of-Stake dynamics. Unlike Bitcoin’s TCP-based connections, Ethereum 2.0 relies on UDP for faster, stateless communication during the discovery phase. This shift supports the complex requirements of a validator-heavy network.
The core of this system is the Ethereum Node Record (ENR) is a cryptographically signed data structure containing node identity, networking information, and consensus-specific attributes. Nodes frequently update their ENRs to reflect changes in their status, such as subnet membership for attestation aggregation. The attnets entry in an ENR defines which subnets a node participates in, ensuring efficient communication for consensus duties.
The discv5 protocol enables nodes to maintain dynamic routing tables that capture comprehensive networking layer information. This adaptability is crucial for handling the constant flux of validators joining and leaving the network. By verifying the cryptographic signatures on ENRs, nodes can trust the authenticity of peer information without relying on a central authority.
Security Implications and Attack Vectors
Peer-to-peer architecture offers significant security advantages. Distributing the blockchain across thousands of nodes makes Denial-of-Service (DoS) attacks difficult to execute successfully. An attacker would need to overwhelm a majority of the network simultaneously, which requires enormous resources. However, peer discovery introduces unique vulnerabilities.
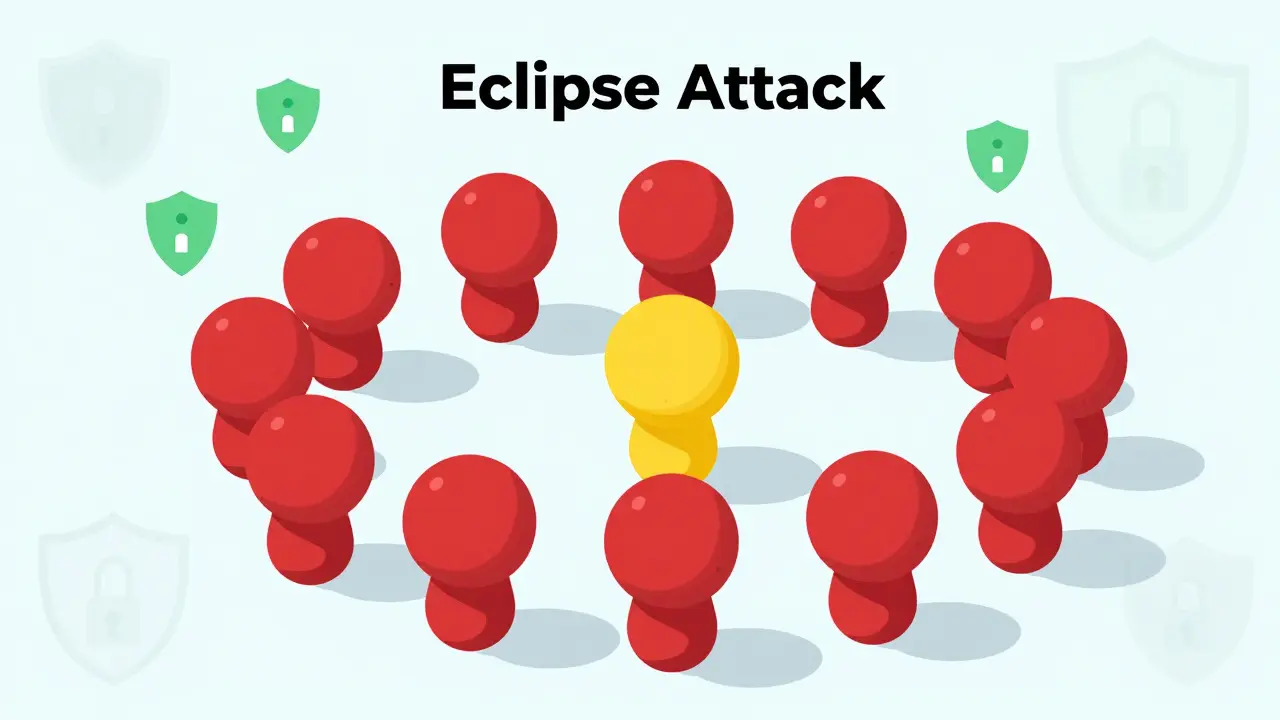
The most significant threat is the Eclipse Attack is a targeted attack where malicious actors isolate a victim node by controlling all its peer connections. If an attacker can manipulate the discovery process to feed a node only fake IPs, that node loses contact with the honest network. It might see a different version of the blockchain, leading to double-spending risks or validation errors. Smaller networks are more susceptible to this than Bitcoin, which benefits from a vast, diverse peer base.
NAT traversal is another challenge. Many nodes operate behind firewalls or Network Address Translation (NAT) devices, making them unreachable from the outside. Protocols must implement techniques like hole punching to allow inbound connections. Additionally, spam and DoS attacks targeting the discovery process itself require rate limiting and reputation systems to mitigate.
What is an Eclipse Attack in cryptocurrency?
An Eclipse Attack occurs when an attacker monopolizes the outgoing and incoming connections of a target node. By controlling the peer discovery process, the attacker isolates the victim from the rest of the network. This can lead to the victim accepting invalid blocks or being unable to broadcast valid transactions, compromising the integrity of the node's participation.
Censorship Resistance and Decentralization
The decentralized nature of peer discovery contributes directly to censorship resistance. In traditional banking, a government or corporation can freeze accounts by blocking access to central servers. In cryptocurrency networks, targeting specific discovery resources rarely stops the network. New seeds emerge, and peer sharing continues through alternative channels.
This resilience extends to payment processing and content platforms. Merchants and creators adopt cryptocurrency payments partly because they cannot be easily de-platformed by third-party processors. As long as nodes can discover each other, the ledger remains open and accessible. This feature is particularly vital in regions with restrictive internet policies or financial controls.
Future Developments in Peer Discovery
As networks scale, peer discovery mechanisms must evolve. Current implementations face challenges during high churn periods, where nodes frequently join and leave. Future developments likely focus on enhanced privacy protection. Techniques like onion routing integration could hide the true IP addresses of nodes, preventing correlation attacks that link transactions to physical locations.
Efficiency improvements are also critical. Larger networks require more sophisticated algorithms to select optimal peers based on bandwidth, latency, and geographic diversity. The ongoing evolution of Ethereum 2.0 demonstrates the need for adaptive protocols that respond to changing validator dynamics. Maintaining decentralization while improving performance remains the central engineering challenge for all cryptocurrency networks.
How do nodes verify the reliability of peers?
Nodes track metrics such as response time, packet loss, and adherence to protocol rules. Misbehaving peers, such as those sending invalid blocks or dropping connections frequently, are penalized or disconnected. Over time, nodes build a reputation score for each peer, preferring connections with proven reliability and speed.
Can peer discovery be improved for mobile devices?
Mobile devices often have limited battery life and unstable connections. Lightweight peer discovery protocols are being developed to reduce overhead. These may involve connecting to lightweight gateways or using compressed address lists to minimize data usage while maintaining network connectivity.
What role do bootnodes play in Ethereum?
Bootnodes are long-running, well-known nodes that serve as initial entry points for new participants. They help bootstrap the discv5 protocol by providing initial ENRs and facilitating the formation of the Kademlia-like routing table used for peer lookup.
Is peer discovery the same for all cryptocurrencies?
No, peer discovery varies significantly. Bitcoin uses DNS seeds and TCP handshakes, while Ethereum 2.0 uses UDP-based discv5 and ENRs. Other networks may use DHTs (Distributed Hash Tables) or specialized gossip protocols tailored to their specific consensus mechanisms and scalability goals.
How does NAT affect peer discovery?
NAT hides internal IP addresses from the public internet, making direct inbound connections difficult. Nodes behind NAT rely on outbound connections to peers or use techniques like UPnP and port forwarding to become reachable. This asymmetry can impact the overall connectivity and resilience of the network.